Wi-Fi Security
Network Security
Enterprise Security
Identity Protection
Virus Protection
Spyware Protection
Spam Protection
Data Protection
Firewalls
Encryption
Virus Removal
Computer - Windows, Apple
Mobile - Apple, Android, Windows
Internet Security
Virus protection alone is no longer enough to keep you safe. You need Internet security. There is a common misconception that viruses and spyware only come in through e-mail. Not so, you can get a virus or spyware by just going to a web site (Trojans secretly load in the background and you never know it).
We protect you when you go on the Internet (both HTTPS and HTTP websites). We also protect you when you go to Facebook and Twitter.
Identity Security / Ransomware Protection
We provide identity protection and phishing protection. This ensures that your personal information such as usernames, passwords, security codes, account numbers and credit card numbers stay protected as you bank, shop and interact online.
We know you cannot afford to have your identity stolen. It now happens every few seconds. It takes years to recover. Identify theft is the number one growing business on the Internet. We also know you cannot have your computer and files locked and held for ransom due to Ransomware.
Our identity protection, firewalls and bank-level encryption keep you safe.
Network Security
We provide secure wired networks and secure Wi-Fi networks for both home and office. We provide mobile protection for your wireless computers, tablets and smartphones.
Enterprise Security / Encryption / Firewalls
One security breach is all it takes to steal your identity, destroy your data, corrupt your programs or shut down your computer.
We provide Enterprise security. We provide Firewalls and strong Secured Socket Layer Encryption (SSL) and Transport Layer Security Encryption (TLS). We provide data protection.

You will never fully recover if you are a victim of cybercrime. Let people
with experience protect you.
We can prevent nightmares from occurring.
You need someone looking out for you. We are security experts that know
what to do to protect your computer, data, identity, network, Internet
use and mobile devices.
Mobile Security
The exploding popularity of smartphones and
tablets has created a major new threat vector -
the mobile application. With the large volume of
apps now available, hackers can easily disguise
and distribute malicious code to unwitting victims.
In fact, apps have become the primary vehicle
to distribute mobile malware, and the exponential growth of apps is compounding the problem.

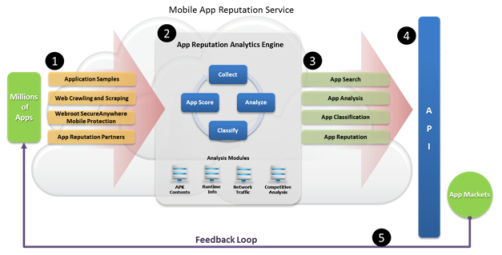
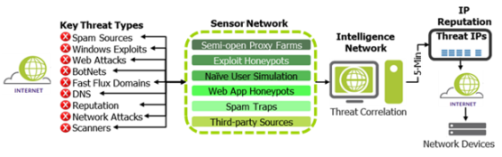
Due to increasing threat presented by mobile applications, we use a third-party Application Reputation Service. Utilizing data collected and analyzed by the Intelligence Network, the Application Reputation Service gives us the ability to manage the delivery of mobile applications that are safe and compliant.
Spyware Security
We can also protect you from the most recent threat; spyware. Most people
don't realize that spyware is being installed on your computer every time
they go on the Internet. Everything you do is being recorded and you are
sending information about yourself. This can then be used by against you.
Further, they can install hijacking software on your computer in the background
without your knowledge that can take control of your computer. This can
damage your computer, as well slow down speed and performance dramatically.
We
get spyware out of your computer so your computer is not hijacked or slowed
down, so you get all the bandwidth you are paying for in your high speed
Internet connections, be it DSL or cable.
Updates
We make sure you are receiving critical updates to your operating system, anti-virus protection, Internet browser and applications keep you current and protected from the latest threats. You are only as good as your updates.
We can create, deploy, and lock down security policies and settings to keep systems up-to-date and properly configured at all times. This allows us to proactively secure workstations before an event can occur, ensuring system uptime and user productivity.

Scalable Cross-Platform Protection

-
Ideal for homes, home offices and small companies
-
Provides advanced, network-wide virus/spam protection and monitoring
- Identity protection
-
Bank level encryption
-
Firewalls
-
Enables enforceable anti-virus/spam and spyware removal policy management across multiple platforms
- Mobile protection for tablets and cell phones
- HTTPS website protection, HTTP website protection, Facebook protection and Twitter protection
-
Ensures system uptime and user productivity by enabling to proactively secure your data, applications, operating system files, incoming e-mail, outgoing e-mail and all workstations before an event can occur
-
Assures rapid deployment and automatic virus protection through reduced virus definition file size and multithreaded rollout
-
Saves your time and reduces administration by offering automatic group management for workstations in the background
-
A variety of options for managing and controlling are offered
-
Volume incentives for desktop workstations
-
Gives smaller organizations the flexibility to leverage their purchasing power in an easy-to-use way
Licensing
We can save you money by licensing. This means you do not have to pay
for a separate copy of the anti-virus program for each computer.
You buy a license for each workstation (costing only a few dollars a month). This saves a home, office or small business thousands of dollars over years. It really adds up.
Virus Protection
Virus protection is the most important protection needed for computers in homes, home offices and business. We provide backend response mechanisms that enable the delivery of fast, reliable, and automatic, hands-free virus detection, analysis, and repairs.
Even with unusually heavy demand for virus/spam definitions during serious outbreaks, our scalable architecture ensures that virus cures will be readily available when needed most. Infected workstations are cleaned quickly and efficiently via on-demand, network-wide virus sweeps.
We will make sure your computer and its' data and your network are virus protected and keep the virus inoculation database constantly updated as new viruses come out.
This is now more important than ever due to the increase in e-mail traffic, since most viruses come in through e-mail.

We also provide extensive scanning and repair solutions that provide the unique ability to update virus and spyware definitionswithout having to reboot workstations, or redeploy application software, thereby easing management. And for extra security, LiveUpdate technology enables your network to configure automatic updates for virus and spyware definitions, including updates for out-of-date definitions.
If you get a virus we make sure you are back up and running fast and are
spared all the hassle and inconvenience. Needless to say, we realize that
your mission-critical data, applications, workstations, server and network
need to be up and running that same day. We will work through the night,
weekend or holidays if need be.
We save you from having to shut down and dismantle your system and haul it to your local service center. We also save the you the drudgery of being without your computer while you wait to get to it back. And finally, we save you from having to drive back to get your computer, load and haul it back to your home or office ...then having to reassemble everything (all while hoping for the best).